4 min read
Post-Quantum Readiness for Mobile Banking: Why CBOM and Crypto Agility Matter for DORA (Part 1)
Cryptomathic : modified on 23. February 2026
- Home >
- Post-Quantum Readiness for Mobile Banking: Why CBOM and Crypto Agility Matter for DORA (Part 1)
Mobile banking apps now sit on the front line of operational resilience. They rely on cryptography for almost everything that matters - user authentication, device binding, secure storage and transaction authorization - at the very moment when today’s public-key schemes (RSA and ECC) are expected to become vulnerable to sufficiently capable quantum computers and “harvest now, decrypt later” attacks.
This first part of a two-part series examines what that shift means for issuers under EU resilience and cybersecurity expectations (notably DORA, NIS2 and the Cyber Resilience Act), and why two practical capabilities are becoming essential evidence of control: a Cryptographic Bill of Materials (CBOM) for the mobile app and a crypto-agile development and operations model that can rotate keys and upgrade algorithms, including a transition to post-quantum cryptography for high-risk use cases. Part 2 will build on this by looking at cryptographic libraries, industry best practices and how to embed crypto agility into mobile architectures.
Regulations explicitly require:
NIS 2, Article 21(1):
- Implement “appropriate and proportionate technical and organizational measures to manage risks posed to the security of network and information systems.”
- Financial entities must ensure their cryptographic technology remains resilient against evolving ‘cryptanalysis and cyber threats’.
- Proactive monitoring is also called out, with reference to ‘threats from quantum advancements’ as a reason why organizations must remain aware and abreast of developments in cryptographic techniques
- Algorithm updates are mandated by DORA, and organizations must have a policy that includes provisions for updating or changing cryptographic technology when threats emerge.
- Adopt “a flexible, risk-based approach to deal with the dynamic landscape of cryptographic threats, including threats from quantum advancements.”
- “Products with digital elements shall be designed, developed and produced in such a way that they ensure an appropriate level of cybersecurity based on the risks.”
DORA RTS (2024/1774), Article 6 and Recital 9:
CRA Annex I Section 1(1):
With a focus on risk management, inventorying, reporting suspected HNDL attacks and resilience testing, the legislation applies stringency to the way financial bodies must consider their readiness.
For issuers of mobile banking apps, this means:
- Maintaining a Cryptographic Bill of Materials (CBOM) for mobile apps that lists all keys and algorithms.
- Understanding the Compliance requirements on these assets (both regulatory requirements but also standard internal compliance requirements to mitigate threats).
- Implementing crypto agility practices in their development framework to be able to rotate keys but also algorithms in due time incl. migration to post-quantum cryptography (PQC) adoption by 2030 for sensitive applications.
- By 31/12/2026: plan PQC migration and set road maps
- By 31/12/2030: “PQC transition for high risk use cases has been completed” - since user authentication (usually based on jwt tokens) and transaction signing (usually based on ECDSA or HMAC) are triggered on mobile apps, it is evident that mobile banking apps will be regarded as high-risk use case.
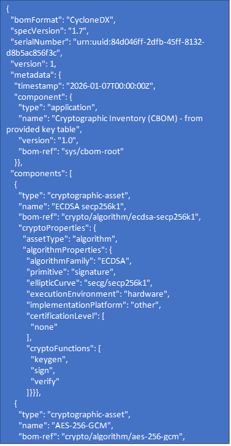
To get started with CBOM, we look at CycloneDX’s (which is the international standard for Bill of Materials for software products) Authoritative Guide to CBOM, which casts light on the importance of it, enabling detailed representation of cryptographic assets within a system. This includes algorithms, keys, certificates, and their relationships to software components. Such granularity allows organizations to assess the strength of their cryptographic implementations and address weaknesses and vulnerabilities like the use of deprecated algorithms or expired certificates.
Most bank CISOs will regard their mobile banking app as very critical since it is now the first media being used to conduct financial operations. Reading the EU coordinated roadmap / NIS Cooperation Group deliverable, this means that they need
Building a CBOM for Mobile Apps
Keys:
The first step in creating a CBOM that shows Crypto Agility and complies to standards and regulations like DORA and NIS2, is to know what libraries, algorithms, certificates, tokens and keys etc are present in your system. The table below shows a sample collection of information about the cryptographic materials used in different parts of a Mobile Payment Wallet application. The list below is indicative only:
|
Key Type |
Key Name |
Purpose |
Algorithm |
Generation Location |
Storage |
Lifetime |
Risk Level |
Recommended Mitigations |
|
Runtime keys |
App Data Encryption Key |
Encrypt cached account data |
AES-256-GCM |
OS Keystore (Secure Enclave/TEE) |
Secure Enclave / TEE |
Persistent |
High |
Hardware-backed storage; restrict export; periodic rotation; require user authentication when accessed |
|
Digital Asset Key |
Protect downloaded statements and media |
AES-256-GCM |
App runtime via OS API |
Keychain / Keystore |
Persistent |
High |
Hardware-backed storage; restrict access; periodic rotation |
|
|
Device Binding Key |
Bind app to device identity |
ECC P-256 |
Secure Enclave (iOS) / TEE (Android) |
Hardware-backed storage |
Persistent |
High |
Hardware-backed; use attestation; do not export; unique per device |
|
|
Transaction Signing Key |
Sign financial transactions (e.g. SCA with DL) |
ECC P-256 |
Secure Enclave / TEE |
Hardware-backed storage |
Persistent |
Critical |
Hardware-backed; require user confirmation; periodic rotation; multi-factor signing |
|
|
SCA Signing Key |
Sign authentication challenges for Strong Customer Authentication |
ECC P-256 |
Secure Enclave / TEE |
Hardware-backed |
Persistent |
Critical |
Key rotation; backup to HSM; zeroize on decommission |
|
|
JWT Signing Key |
Sign JWT tokens for session and API token integrity |
RS256 / ES256 / Ed25519 |
Server-side in HSM |
HSM (private) / App bundle (public) |
Persistent |
High |
Rotate keys regularly; short token lifetimes; validate signatures |
|
|
Attestation Key |
Device attestation (e.g. SafetyNet, DeviceCheck) |
ECC P-256 |
OS-managed attestation service |
OS-managed |
Persistent |
High |
Use platform attestation APIs; periodic re-attestation; validate responses server-side |
|
|
Session Key |
Encrypt session data |
AES-256 |
Runtime (ECDH handshake) |
Memory only |
Ephemeral |
Medium |
Zeroize after use; ephemeral lifetimes; derive via strong key exchange |
|
|
TLS Handshake Keys |
Secure channel establishment |
ECDHE P-256 then AES-256 |
OS TLS stack |
Memory only |
Ephemeral |
Low |
Use up-to-date TLS libraries; check certificates; ephemeral keys per session |
|
|
Push Notification Token |
Authenticate push messages |
ECC P-256 |
Server (APNs/FCM) & stored by app |
Application storage |
Persistent |
Medium |
Keep token confidential; refresh regularly; validate sender |
|
|
Credential-Derived Key |
Protect offline login data |
AES-256 |
Derived from user password on device |
Keychain / Keystore |
Persistent |
High |
Use strong KDFs with high iteration count and salt; enforce strong password policies |
|
|
Supply Chain Key |
App Signing Key |
Sign APK/IPA to ensure authenticity |
RSA-2048 / ECC P-256 |
Developer build environment / Apple PKI |
HSM or secure build environment |
Persistent (until expiration) |
Critical |
Keep private keys offline; store in HSM; restrict access; rotate certificates |
|
App Integrity Verification Key |
Verify app code and update integrity |
RSA-2048 / ECC P-256 |
Server-side (developer infrastructure) |
Public key in app; private key stored in secure server context |
Persistent |
Medium |
Secure private key on server; sign code via HSM; verify signatures on client; rotate keys periodically |
|
|
Wallet keys |
Wallet Private Key |
Sign ERC-20/CBDC token transactions |
ECDSA P-256 |
Secure Enclave / TEE |
Hardware-backed storage |
Persistent |
Critical |
Hardware-backed storage; require user consent for each operation; consider multi-sig; backup securely offline |
The assets marked in purple are outside of your control (apple or Google)
The assets marked in green are typically handled on the server side.
The assets marked in orange are assets which you need to control on your app development lifecycle
A snippet from a CBOM for a Mobile Payment Wallet could look like this for a particular algorithm or key:
In this first part, we have focused on why EU regulations and the EU PQC roadmap make a CBOM for mobile banking apps essential, and how to start inventorying keys and algorithms. In Part 2, we will build on this foundation by looking at cryptographic libraries, compliance frameworks and how to achieve practical crypto agility for mobile banking under DORA and NIS2.
Future-proof your mobile app security architecture – Learn how to defend against AI-powered attacks, implement crypto agility, and build quantum-resilient mobile banking infrastructure. Download the guide now.