2 min read
Key Block Conversion: Techniques, Methods & Examples
 Martin Rupp (guest)
:
modified on 15. July 2022
Martin Rupp (guest)
:
modified on 15. July 2022
- Home >
- Key Block Conversion: Techniques, Methods & Examples
There are several types of key block formats used in different industries, especially the retail banking industry. The systems that use these key blocks are part of heterogeneous networks. Therefore, they need to interchange their data with other systems, potentially using different key block formats or even different key binding algorithms (key wraps, key encapsulation, etc.). In what follows, we will explain how this is possible and what techniques are used to perform that.
Overview of the Problem
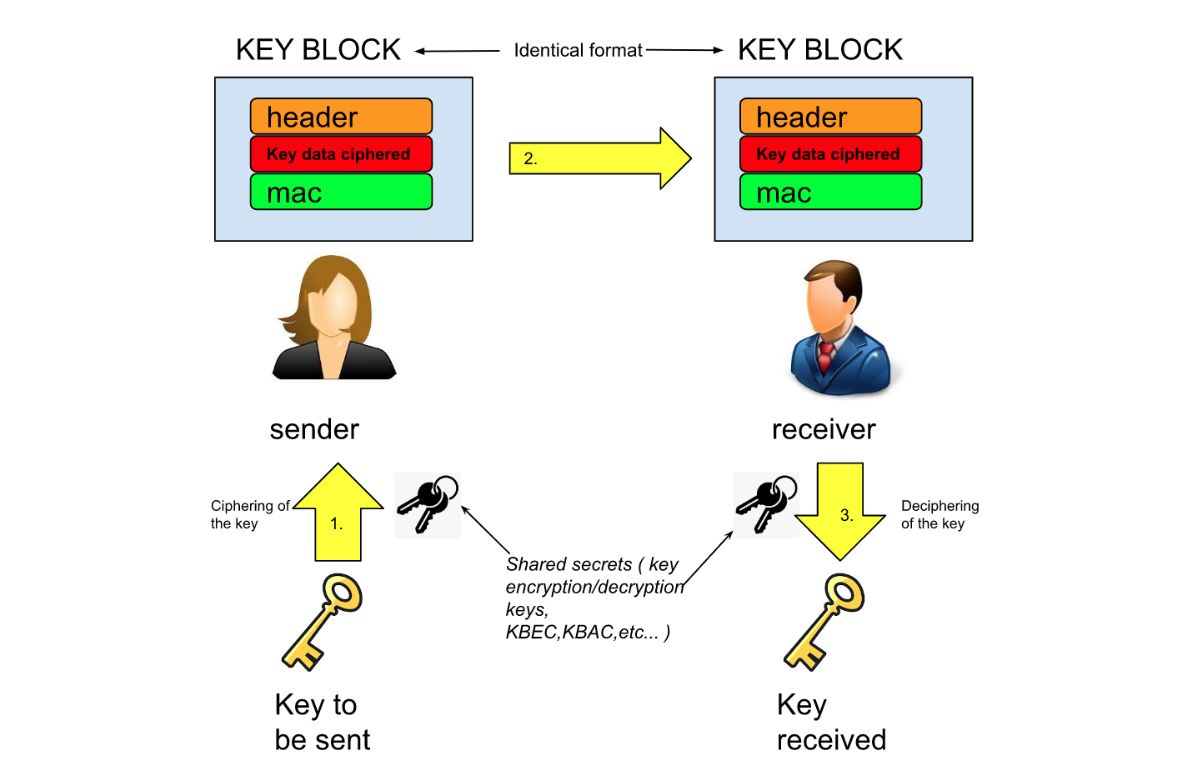
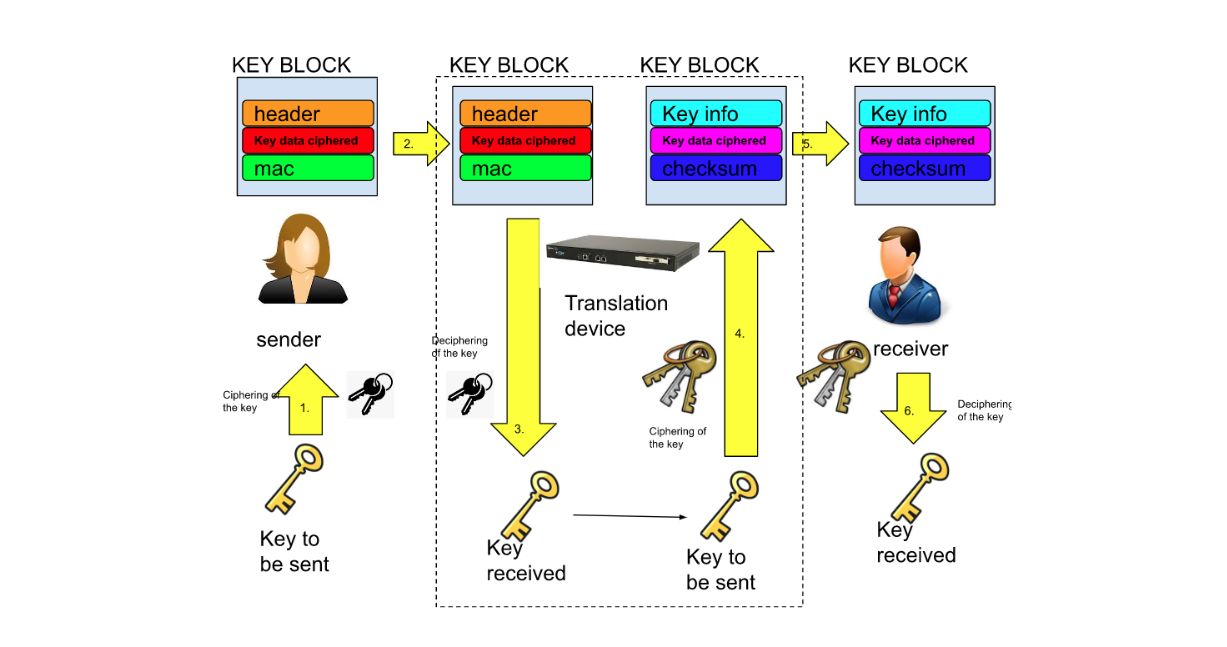
Key blocks are special cryptographic structures that allow the transmission of key material over what might be unsecure networks and environments. They are sent from a sending party (“sender”) to a receiving party (“receiver”).
The sender and receiver usually have a shared secret. This is often a symmetric encryption key that allows the relevant party to cipher and decipher the key blocks.
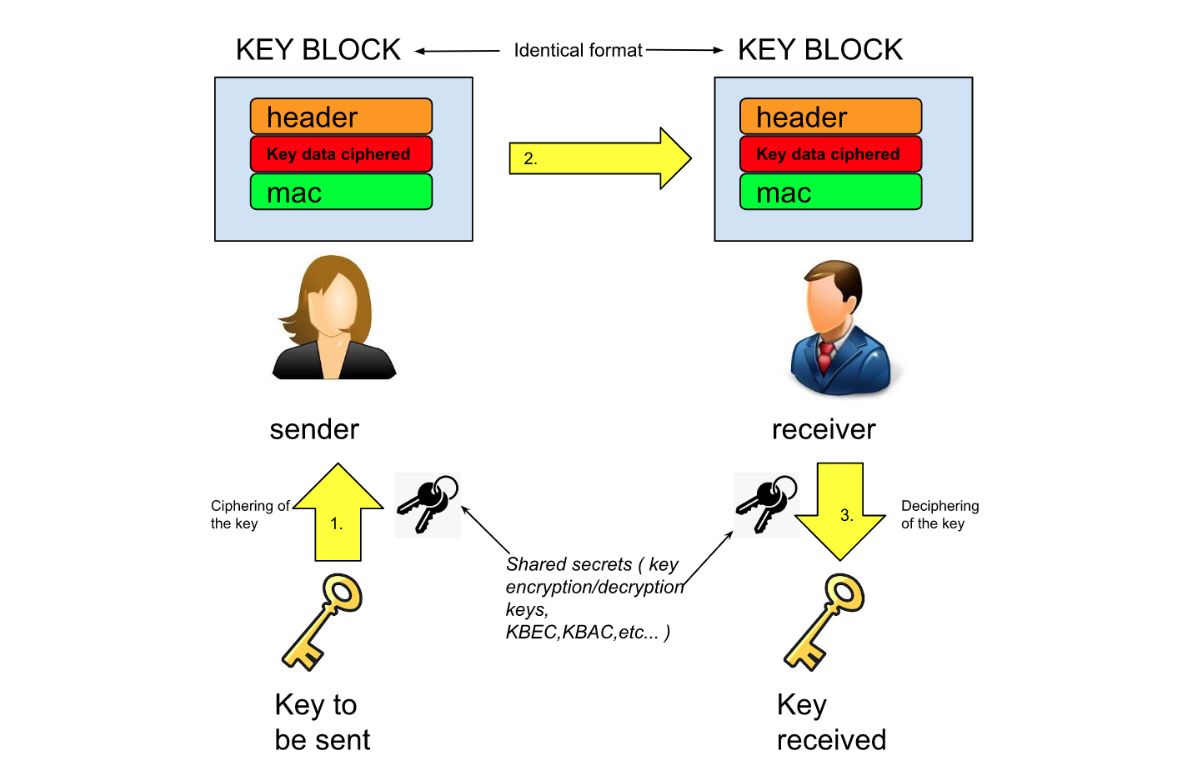
If the sender and the receiver share the same format for a key block, then the operation is simple enough. The receiver will know how to retrieve the key data from the key block of the sender. This is typically the case if the sender and receiver are part of the same organization (for example, the same bank).
But things are not always so ‘simple’. Different organizations will use different key block formats. In fact, they might also not share the same secrets, such as key block encryption/decryption keys, etc. There could be different algorithms and different ciphers used for key encryption, different offsets for the header of the key block, and potentially more differences.
In such a situation, how can keys still be securely exchanged inside such insecure and heterogeneous environments?
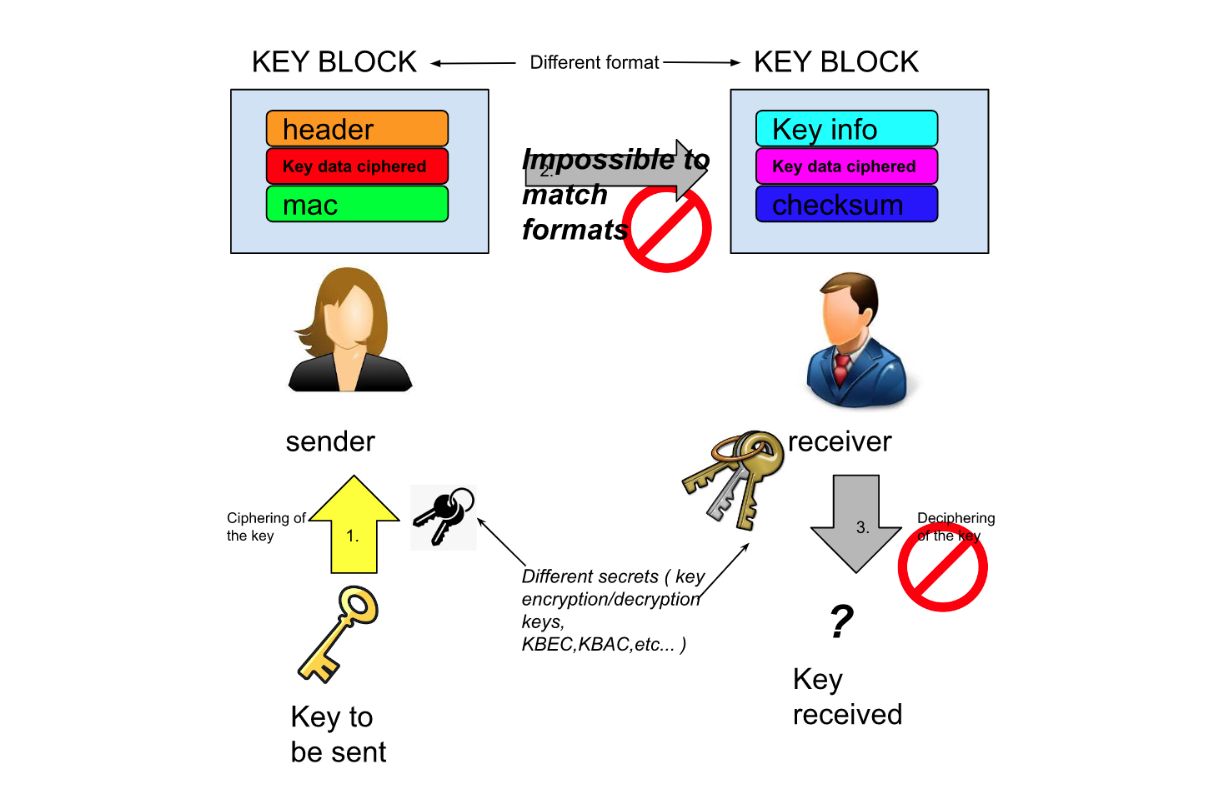
Key Block Translation Devices
Key block translation devices are designed to solve the problem of translating key blocks. Typically, they are HSMs (hardware security modules). Such devices can convert one key block from a given format into another format.
These translation devices act as “trusted middlemen” between the different heterogeneous networks. They will contain the encryption and decryption keys of both the sender and the receiver. Of course, since they will decipher a key and re-cipher it, they must do it in their own ultra-secure environments.
There is a wide variety of key block formats. It’s not always possible to convert all formats to other formats because some formats may contain information that makes little sense in the other format. It’s mostly industry-driven, depending on the demand.
Some key blocks may be different, but still follow the TR-31 implementation document. This provides some guarantee in terms of interoperability. However, some other formats may be really ‘exotic’, at least to each other. That is why there is no universal translator between key blocks.
Here we list some sample key block formats that are usually converted between each other by major HSM brands:
- Atalla key blocks
- Thales key blocks;
- IBM (CCA) key blocks
- TR-34 key blocks.
Payment Networks Example
In payment networks, PINS are usually ciphered and sent to the issuing bank for cardholder verification within a key block. It’s also now fully mandatory to do this according to the latest PCI PIN requirements. The problem is that a payment terminal, like an ATM, will use their own keyset and potentially their own key block format to do this. The issuing banks do not specifically know how to decipher the key block sent by the ATM and rarely have the right keyset to do this (unless the issuing bank of the cardholder operates the ATM). Therefore, the payment networks need key block translation devices to operate. They are more precisely named PIN translation devices. As usual, they are almost always HSMs.
Here we show a minimal flow involving PIN (key block) translation devices. The flow consists of the:
- Acquiring bank (and its ATM)
- Processor (here Visa)
- Issuing bank
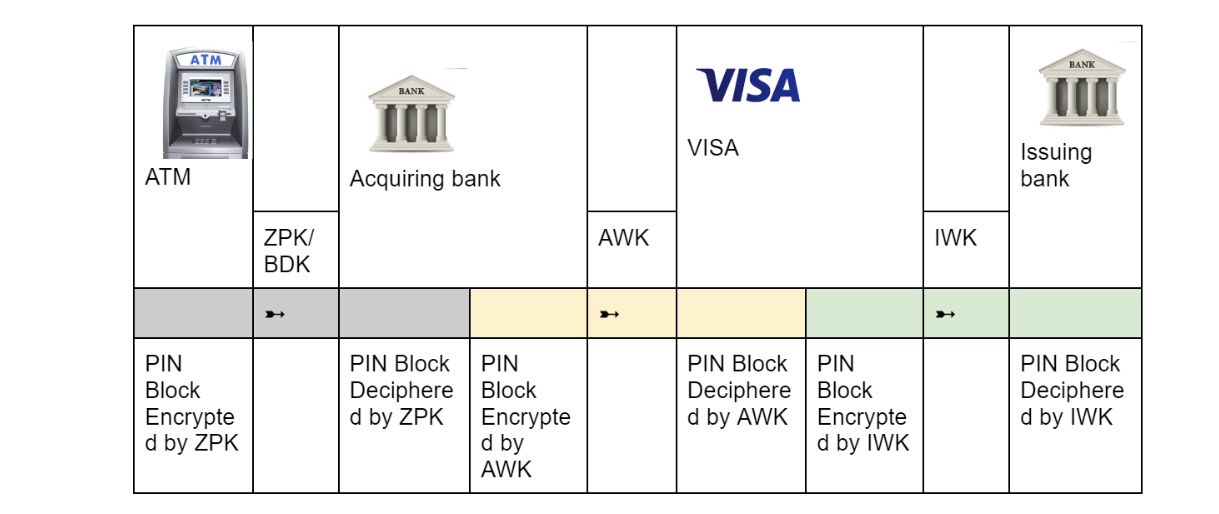
As shown above, the PIN block is indeed ciphered between the HSMs of the different zones and never travels unencrypted outside the security modules.
For decades, Cryptomathic has been a major player in the payment network landscape. Cryptomathic automates key management for banks across payment networks and supports all major industry-compliant key blocks.