3 min read
AWS External Key Store: Crypto Gateway Integration
 Glen Leonhard
:
modified on 22. June 2023
Glen Leonhard
:
modified on 22. June 2023

- Home >
- AWS External Key Store: Crypto Gateway Integration
AWS Key Management Service (KMS) has long provided cryptographic services to safeguard your AWS resources. This involves generating and managing keys in a straightforward setup. This system functions effectively for conventional applications not subject to regulated workloads.
To offer more control over the lifecycle of keys, AWS introduced the Bring Your Own Key (BYOK) functionality. While BYOK is a substantial expansion to the KMS suite, it necessitates several manual tasks and only enhances the encryption of the actual data keys.
AWS External Key Store and the Introduction of HYOK
The most recent innovation in this space is the AWS External Key Store (XKS). This feature introduces the Hold Your Own Key (HYOK) concept and effectively presents a comprehensive platform for managing the entire encryption life-cycle.
Integration of AWS XKS with Cryptomathic’s Crypto Service Gateway (CSG)
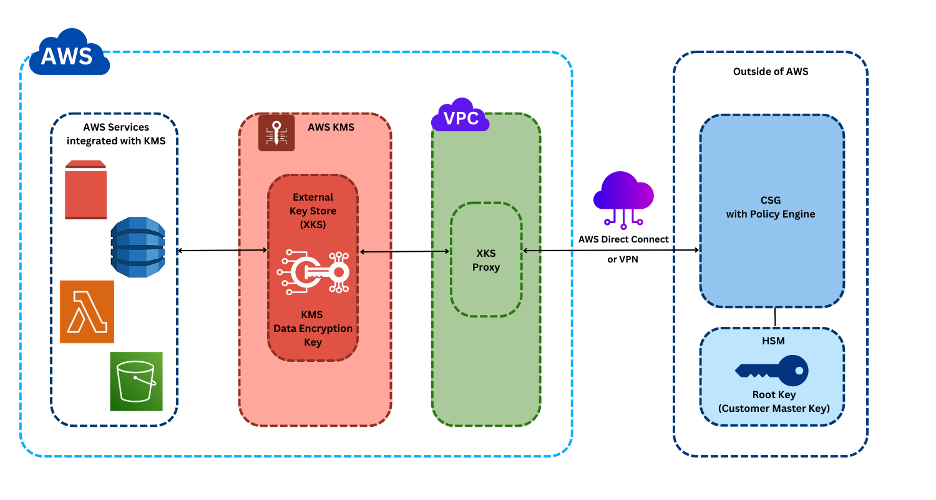
In combination with Cryptomathic’s Crypto Service Gateway(CSG), AWS XKS offers a more streamlined and secure cryptographic engine as an external key manager through the XKS feature. Utilizing CSG as an external key manager provides organizations with absolute control over their keys, enabling their usage in multi-region/multi-cloud environments, on-premises, or in hybrid applications and service deployments.
Workflow of CSG with AWS KMS and XKS Proxy
The connection from AWS KMS to an external key manager is achieved via a specialized XKS Proxy. This allows the CSG to act as a central kill-switch if needed in a situation where organizations would wish to suspend data encryption or decryption at AWS resources.
The journey of an encryption or decryption request begins when an AWS resource generates such a requirement. This request is then directed through AWS KMS, which subsequently forwards it to the XKS Proxy. Once received, the XKS Proxy takes on the crucial task of translating this request into specific operations that are compatible with Cryptomathic’s Crypto Service Gateway (CSG) interface.
Acting as an external key manager, the CSG interface receives these operation-specific requests and gets into action. The CSG harnesses a pool of FIPS 140-2 level 3 Hardware Security Modules (HSMs) to execute these operations. It is within these HSMs that the Root Keys (also known as AWS Customer Master Keys) are securely stored, ready to be used for encryption or decryption processes.
Once the CSG completes the execution of the requested commands, the outcomes, or responses, are dispatched back through the same chain, but in the reverse order. This means the responses make their way back to the AWS resources via the XKS Proxy and AWS KMS, ensuring a smooth, efficient, and secure loop of command execution and response delivery.
This entire process ensures that the integration between AWS KMS and the external key manager (CSG) is seamless, robust, and reliable. It not only provides a secure path for the encryption and decryption requests but also ensures that the AWS resources receive the responses they need without delay, contributing to a highly efficient and secure data encryption infrastructure.
Multi-Region Key Management with CSG
Moreover, CSG's scalable infrastructure allows it to act as an external key manager for multiple AWS regions and unique KMS instances, a valuable feature for organizations aiming for key and data encryption operations segregation, yet still desiring centralized external key management.
Client Benefits of Using AWS XKS with CSG
- Speed and reliability: AWS XKS requires the security proxy to respond within 250 milliseconds (ms), even during peak cloud-based infrastructure performance. Cryptomathic XKS proxy ensures scalability to any level, excellent performance, and budget-friendly operations.
- Privacy law compliance: With compliance regulations such as the CCPA, GDPR, and the Privacy Act, navigating the compliance landscape can be challenging. Cryptomathic XKS helps businesses stay compliant effortlessly.
- Centralized policy control: CSG provides policy enforcement that enables security teams to exercise stringent control over who can use keys and the specific parameter choices for all operations centrally.
- Detailed logging: CSG generates extensive tamper-evident logs for auditing and regulatory purposes, recording who used a key, when it was used, and what cryptographic operation was performed.
In short, AWS KMS and Cryptomathic's CSG integration provides a solution that is faster, more reliable, compliant, and offers centralized control over key management, making it a must-consider for all organizations seeking to strengthen their data security measures in the cloud.
Interested in learning more? Download the AWS XKS solution brief or reach out to Cryptomathic today. Our team is ready to assist you with our innovative and reliable data encryption solutions. Your data security is our priority. Contact us now!