3 min read
Challenges in Key Management for EMV Personalization
 Martin Rupp (guest)
:
modified on 20. September 2022
Martin Rupp (guest)
:
modified on 20. September 2022
- Home >
- Challenges in Key Management for EMV Personalization
The EMV personalization data processing in itself is not the topic of this article, we will instead focus on the cryptographic schemes involved in EMV personalization, as well as the key management involved; which is both complex and mandatory.
EMV personalization relates to the process of writing specific information to the chip of a payment card. These data are most often of cryptographic nature and involve secure and confidential data transmission between the personalization devices and the chip of the cards. The requirements for EMV personalization is ruled by a global document named the CPS, for ‘Common Personalization Specifications’ or alternatively for ‘Card Personalization Specifications’ [1] which contains the main guidelines for personalizing an EMV payment card. Additionally, card schemes often have their own specifications and requirements. For instance, Visa maintains the VISA Global Personalisation Requirements (GPR).
Introduction
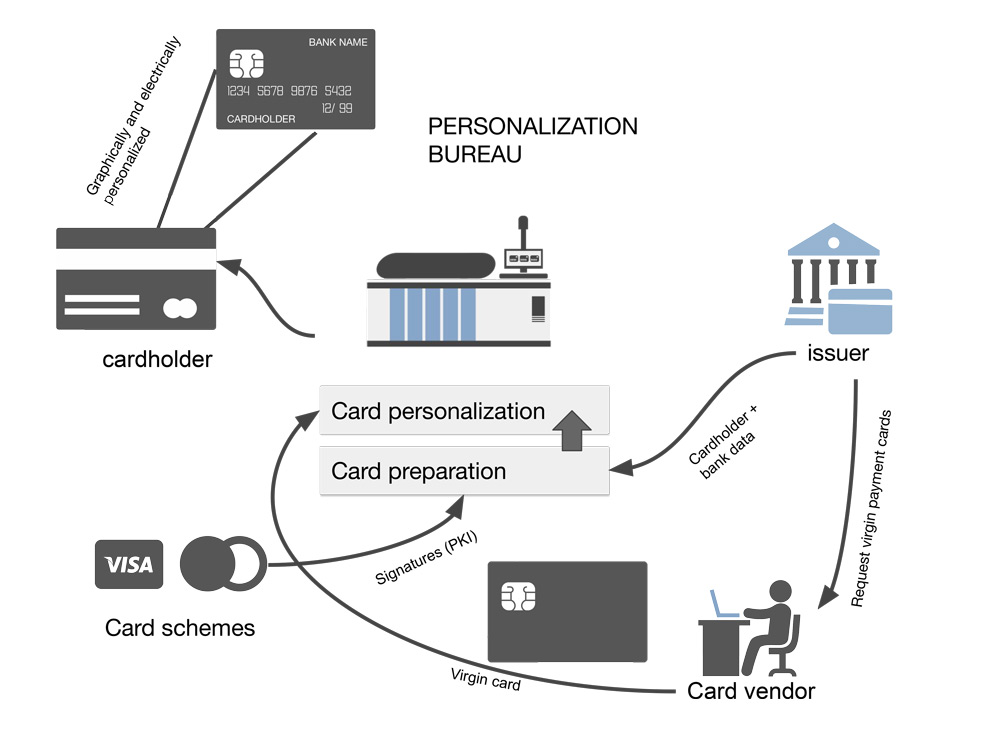
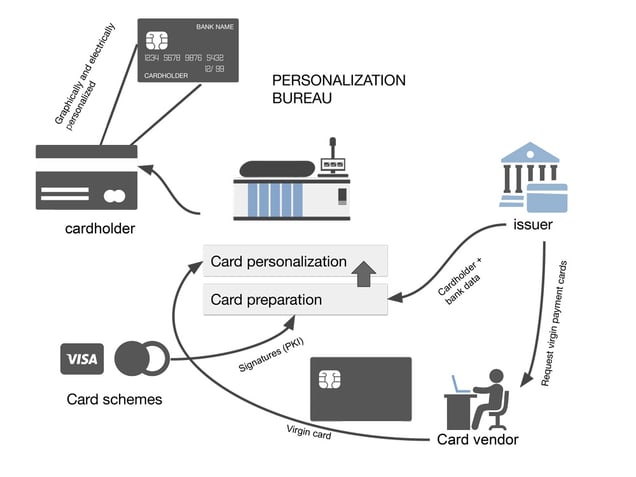
First, we need to introduce the main actors involved in a typical EMV personalization process:
The person who is authorized to use a payment card delivered by the issuer. This is generally a client of the issuing bank (issuer).
- The issuer
As described in the four-corner model, an issuer is a financial organization that produces (‘issues’) EMV payment cards.
- The personalization bureau
The entity that defines the data that will be used to personalize a payment card profile. Typically they also act as a data preparation center and a personalization center, but not always.
- The data preparation center
This is where the data is collected and prepared. A file produced by the personalization bureau (card personalization data file) is processed together with a card profile by an EMV data preparation system.
- The personalization center
Where the personalization physically takes place. E.g. the environment where payment cards are inserted into couplers and where data is written to the memory. (only for contact cards)
- The card integrator (or card vendor)
A trusted third party that manufactures and programs the chip of the payment cards on behalf of the issuer.
- The card scheme
This is also known as a card brand, e.g. Visa, Mastercard, etc.
In contactless personalization, also known as over-the-air (OTA) personalization we must also consider the additional following actors:
- The token services providers (TSP)
This is a trusted third party that provides tokenization
- The trusted service managers (TSM)
This is a trusted third party that provides OTA personalization services, e.g. connecting remotely a personalization center to a secure element.
There are in fact more actors but as we can see the ecosystem is already quite complex. It is also worth noting that some entities may play several roles. For example, issuers may also be the ones who do the data preparation.
Let us look in more detail at the role of each party.
Personalization Bureau
There are two aspects in a card personalization: the most obvious is ‘feeding’ the data (cardholder data, bank data, keys…) and formatting them, securing them and getting them written to the virgin payment card but there is a second aspect that is less obvious.
With the EMV card, a card issuer must define the configuration of the EMV parameter settings. There are more than a hundred of such parameters which will define the ‘rules’ of a transaction and how the card should behave: if a transaction should be authorized online or offline, how many PIN tries there can be, how the card should handle risk management and so on. Because of the great complexity involved in the combinations of all these parameters, card profiles can be very different, even if the same payment applications are used.
The definition of a card profile is highly important for an issuer and it’s often a delicate and difficult matter. The issuer is usually totally involved in the decision process which is conducted with experts from the personalization bureau. Such a personalization bureau can be run by the card vendor or by the issuer itself.
Data Preparation Process
The data preparation process consists of generating a specific EMV personalization file from the issuer’s card personalization data file. The output has to be transferred securely to the card personalization center, either because an HSM containing the data is directly attached to the machines of the card personalization center, or via a secure channel using both encryption and authentication. The CPS [1] makes a difference between the direct or indirect personalization methods. In the indirect cases, two distinct zone keys are involved meaning two secure channels transporting the data from the data preparation to the personalization device (e.g a coupler) and from that personalization device to the IC card. This means that transport keys have to be involved.
The card personalization center
The card personalization center is a highly-secured area usually protected by conditional access video monitoring and security guards. The card personalization center continuously receives the order from issuers and processes them automatically into batches. They maintain warehouses with all the necessary material to ship the cards once they are personalized. The center must respect a very strict policy and follow specific security rules. Without such rules, malevolent people could access the cards and perform some manipulations or access secret data. For instance, it must be strictly impossible for an intruder to insert spy devices in between the electronic personalization device (‘coupler’) and the chip itself. However even if such devices were installed, the sensitive data would still be protected because they are ciphered between the coupler and the chip.
It has to be noted that the card vendor is responsible for the so-called ‘pre-personalization’ of the card: loading eventually an operating system and a Global Platform compliant system and all data needed for the card system to operate but without specific ‘banking’ information.
Conclusion
EMV card personalization involves a complex ecosystem. In the next parts, we will see in detail the cryptography involved with EMV personalization and finally we will explain why secure key management is mandatory (required by the card schemes) for EMV personalization and how it works in such a context.
References and Further Reading
- [1] EMVco. Card Personalisation Specification Version 2.0, August 2021