4 min read
Key Management Systems: Top Capabilities & Functions
Cryptomathic : modified on 29. June 2015
- Home >
- Key Management Systems: Top Capabilities & Functions
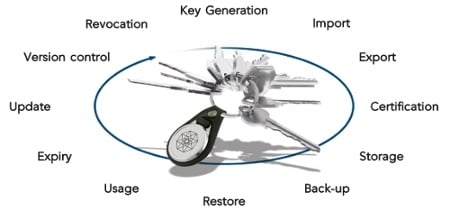
Typical Services Provided by Key Management Systems
Key management is the administration of tasks involved in all aspects of cryptographic key usage in a cryptosystem. This includes dealing with the generation, distribution, exchange, storage, use, and replacement of keys. All aspects of security should be covered for the life-cycle of a key, from key generation to replacement, storage, or disposal. Each key must also be protected during its life-time to prevent unauthorized disclosure, modification, substitution, replay, and improper use. Likewise, the functions used in key management must be prevented from such unauthorized use.
Each Management Requirement is Unique
There is no universal solution for key management that will work for all businesses and other types of institutions, companies, etc. Each system may have its own criteria for information security, including type of network topology, cryptographic services, and algorithms. Government and company rules and regulations also need to be taken into account. This requires tight coordination between encryption enabled storage devices and key management, in order for security policies to be effectively enforced.
Phases of Design
There are many phases involved when designing and implementing a key management system. They could include cryptographic algorithm design (including modes of operation), protocol design, interaction with key servers, user procedures, implementation procedures, verification procedures, etc. Each of these phases should be thoroughly scrutinized and evaluated to ensure that the cryptographic mechanisms provide the desired security level.
 Difficulties to Overcome
Difficulties to Overcome
The security of any cryptographic system is mostly dependent on the level of security provided by the keys themselves. Therefore, successful key management is critical to the security of the system. In practice, management of the keys is the most difficult aspect of cryptography, because it involves system policy, user training, organizational and departmental interactions, and coordination between all of these elements. The basic encryption and storage of keys is not hard, but getting the right keys to the authorized users and managing the lifecycle of the keys is the challenging part. The sheer volume of data transactions and distributions within storage media within large companies make key management a formidable task, because of the millions of keys that need to be generated, handled, protected, stored, replaced, and disposed of when needed. The fact the some companies use different encryption tools (possibly incompatible), make the management tasks even more formidable. Key management becomes even more difficult in a Cloud environment, where many other types of transactions can occur, and a third party is sometimes involved.
Main Issues in Implementation
The main issues that must be faced when implementing a key management system are:
- Complex Management: How to manage and control encryption keys numbering in the millions.
- Security Issues: How to sustain a protection level from outside hackers/malicious insiders.
- Data Availability: Making sure data is available to authorized users.
- Scalability: How to support multiple databases, applications and standards.
- Governance: How to keep management functions according to policy rules and regulations.
Important Security Measures
Since most modern security systems use a combination of symmetric, asymmetric, and possible hybrid methods for key usage, the requirements for key management functionality will vary depending on the method. In any case, the most important security measures that need to be considered when implementing a key management system include:
- Data confidentiality: keys and other data are kept confidential when transmitted or stored.
- Modification detection: Maintain integrity be countering the threat of modification of data
- Replay detection/timeliness: detect if old data has been inserted into current data or storage
- Entity authentication: verify that identities are as claimed.
- Data origin authentication: verify the source of a message is as claimed.
- Nonrepudiation of Reception: proof that a message was actually received.
- Notarization: register messages to attest content and origin.
Services Provided
Some of the services that a key management system should provide to maintain these security measures include:
- Entity Registration: establish a registry of identities/credentials to allow authentication to the system.
- Key generation: the producing of keys that are of sufficient quality, secure, and not predictable.
- Certification: issue certificates for authentication purposes.
- Authentication/Verification: verify identities; three basic types:
- entity authentication
- message content authentication
- message origin authentication
Several key distribution functions should be included in a key management system, which securely provide keys to parties requiring them.
- Encipherment: key may be protected by encrypting with another key
- Modification detection codes: add redundancy to detect changes whether accidental or malicious
- Replay detection: measures to detect an attempt to foist off an old message as current
- Proof of knowledge of the key: allows proving that a party has and is able to use the key (e.g., challenge/response)
Most other functions are used for key maintenance, which will preserve, protect and dispose of keys as needed.
- Key Storage: secure memory locations for protecting and accessing keys.
- Key Replacement: update or renew the key and associated parameters when stale or compromised
- Recovery: re-establish keys lost through human error, software bugs or hardware malfunction
(Key deletion and archival are also maintenance functions, but these are listed as states in the following list.)
Possible Key States
In order to get a better idea of the functionality of a key management system, it’s important to know the various states that a symmetric key or public/private key pair can exist in. As functions are performed, keys will make a transition from one state to another. (Note that some key management systems may not use all of these states, and other systems may add additional states.)
- Generation: A symmetric key or public/private key pair is generated when required
- Activation: A symmetric key or private key is activated when it is required to be used. (A public key is activated when it is made available or on the date indicated in its associated metadata.)
- Deactivation: A symmetric key or private key is deactivated when it is no longer required for applying cryptographic protection to data. A public key is not deactivated. It may expire, be suspended, or revoked.
- Suspension: A key may be suspended from use for a variety of reasons, such as the key owner being temporarily away.
- Expiration: A key may expire due to the end of its crypto period.
- Key Deletion: securely destroy keys no longer needed
- Key Archival: : The key is set aside in long term storage if it is no longer needed for normal use, but may eventually be reviewed ( mostly for notarization or non-repudiation).
- Revocation: A revocation applies only to public keys, but the corresponding private key(s) are also revoked.
References:
CS361C: Information Assurance and Security
Cryptographic Key Management Issues & Challenges in Cloud Services