2 min read
How to Use a Centralized KMS to Enforce Information Security Policies
A Key Management System (KMS) must be designed in a manner that supports the goals of each organization using the KMS. The aim of a security policy...

2 min read
A Key Management System (KMS) must be designed in a manner that supports the goals of each organization using the KMS. The aim of a security policy...
5 min read
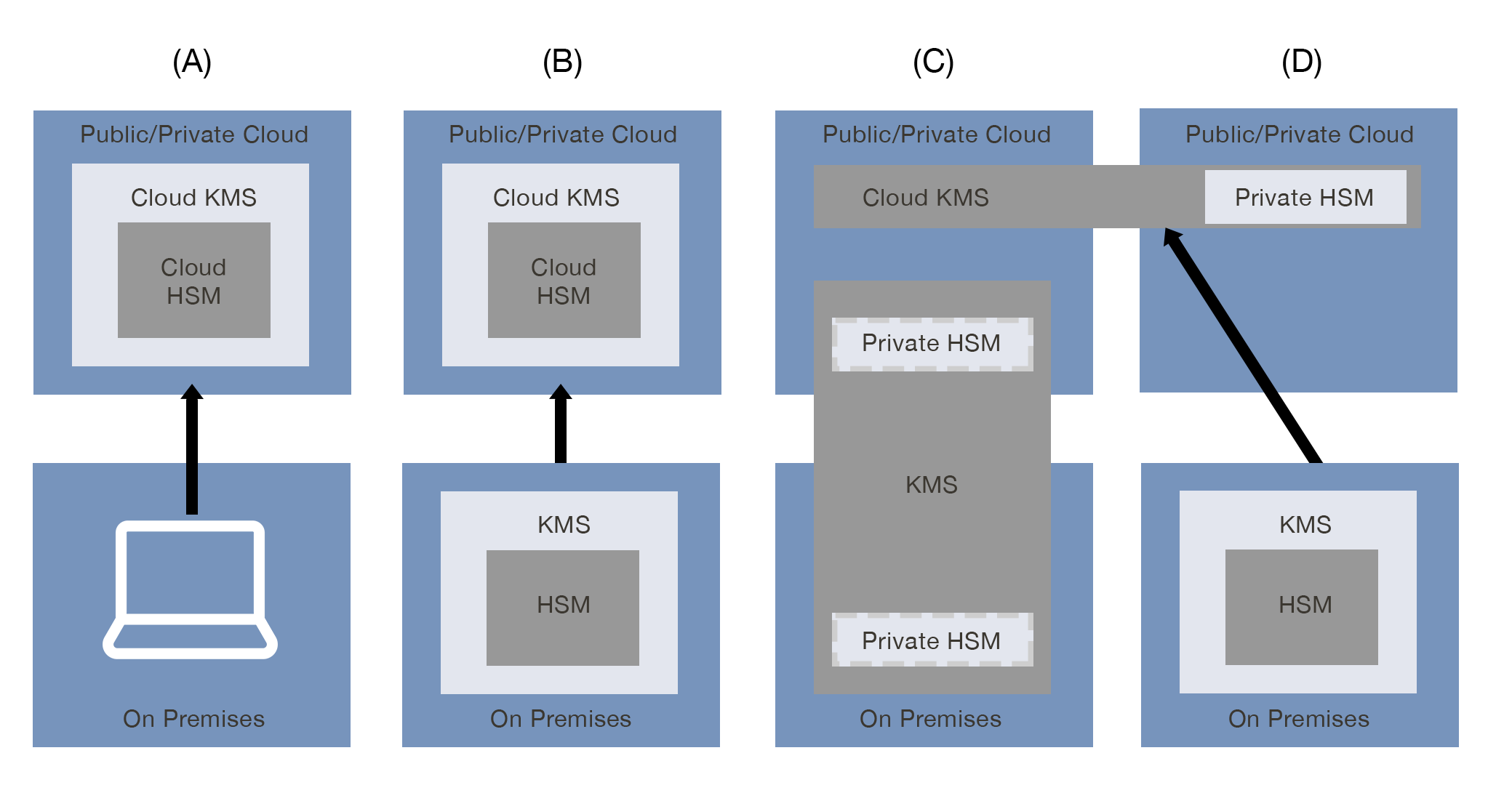
This article explains the four primary cloud KMS pattern combinations and which are best suited for use with Cryptomathic’s Key Management System...

2 min read
The use of cryptography is the foundation for the secure processing of financial and other electronic transactions. On the other hand, the management...

3 min read
A study published in early 2018 by the European Union Agency for Network and Information Security (ENISA), revealed that 90% of the respondents...
3 min read
The PCI Council requires most actors of payment networks to implement ANSI X9.24/TR-31-compliant key blocks to wrap and securely transmit, transfer,...

5 min read
RSA, a short recap In a public key scheme, and for the sake of simplicity, assume a public scheme based on encryption-decryption (as opposed to e.g....

2 min read
User interface design and usability are the deciding factors in attaining a good user experience for most IT deployments, including key management...

3 min read
Bring your own key (BYOK) is a popular term relating to key management for cloud applications. However, a lack of standardization makes it confusing...
4 min read
Banks continue to feel the profound transformational effects that digital technologies have on their business. This can be seen in the creation and...