4 min read
What is Quantum Computing And How Will It Impact Cybersecurity?
For years, there has been persistent chatter that quantum computing is coming and that organizations should be prepared for its arrival. But what...

4 min read
For years, there has been persistent chatter that quantum computing is coming and that organizations should be prepared for its arrival. But what...

3 min read
The phrase “…Software is eating the world.” was famously used by Marc Andreessen in a WSJ article in 2011. No one could argue that software has...

2 min read
The eIDAS Regulation (No 910/2014) (EU eIDAS) came into force in 2016. It created a Europe-wide legal framework for electronic identification,...

5 min read
There is no question that quantum computing is coming. However, organizations need to question themselves as to whether they will be vulnerable to...
3 min read
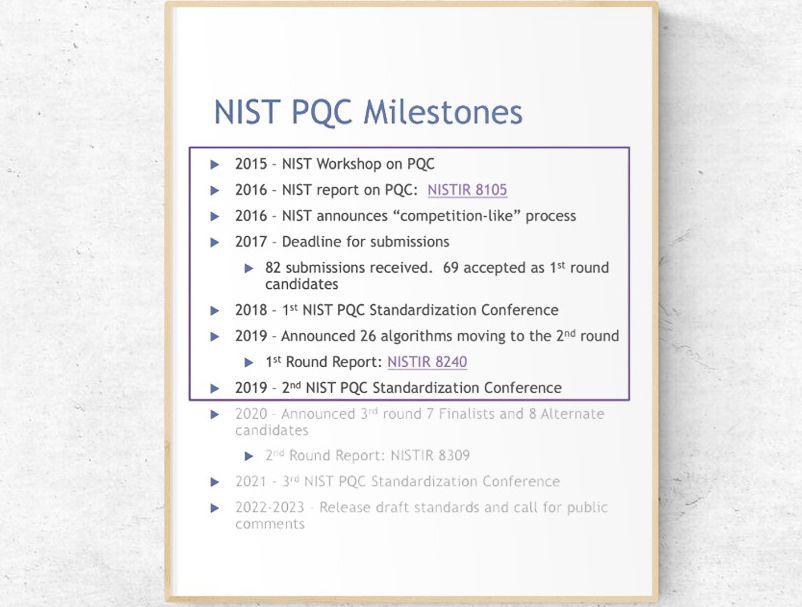
Most current public-key cryptography (asymmetric) algorithms are vulnerable to attack from large-scale quantum computers. In its efforts to...
2 min read
Maybe you have wondered where our logo comes from and what it actually means. If you have, we hope the following will answer these questions. Just as...

3 min read
As the scientific community continues to push towards achieving quantum computing on a mass scale, smart companies are busy making preparations for...

2 min read
Attacks on mobile banking and payment applications frequently begin with the use of an emulator for the mobile operating system, where the targeted...

6 min read
The ever-growing number of applications and uses for mobile devices has long been a hot topic. Using mobiles to electronically sign transactions and...